Identity Fusion Blog: PrivilegedAccessManagement
Breach Detection Takes Too Long: Why Even “New” IAM Systems Need Modernization
IBM’s research lays it bare: it takes 292 days on average to detect a compromised non-human identity (NHI). That’s nearly 10 months, an eternity in the digital battlefield. By..

The Genius Behind Security
I often write about the challenges that define cybersecurity today, the relentless push and pull between defenders and attackers, the fragile balance between Identity and Access..

Where to Begin the Zero Trust Journey: Securing IAM with Least Privileged Access
Today organizations must come to terms with a stark truth, the perimeter is gone. Old security thinking offers little to no protection in this borderless realm. If you're still..
%20Management%20.png)
The State of Non-Human Identity (NHI) Management
As digital ecosystems grow increasingly complex, so too do the identities operating within them. No longer confined to human users, identity and access management (IAM) strategies..
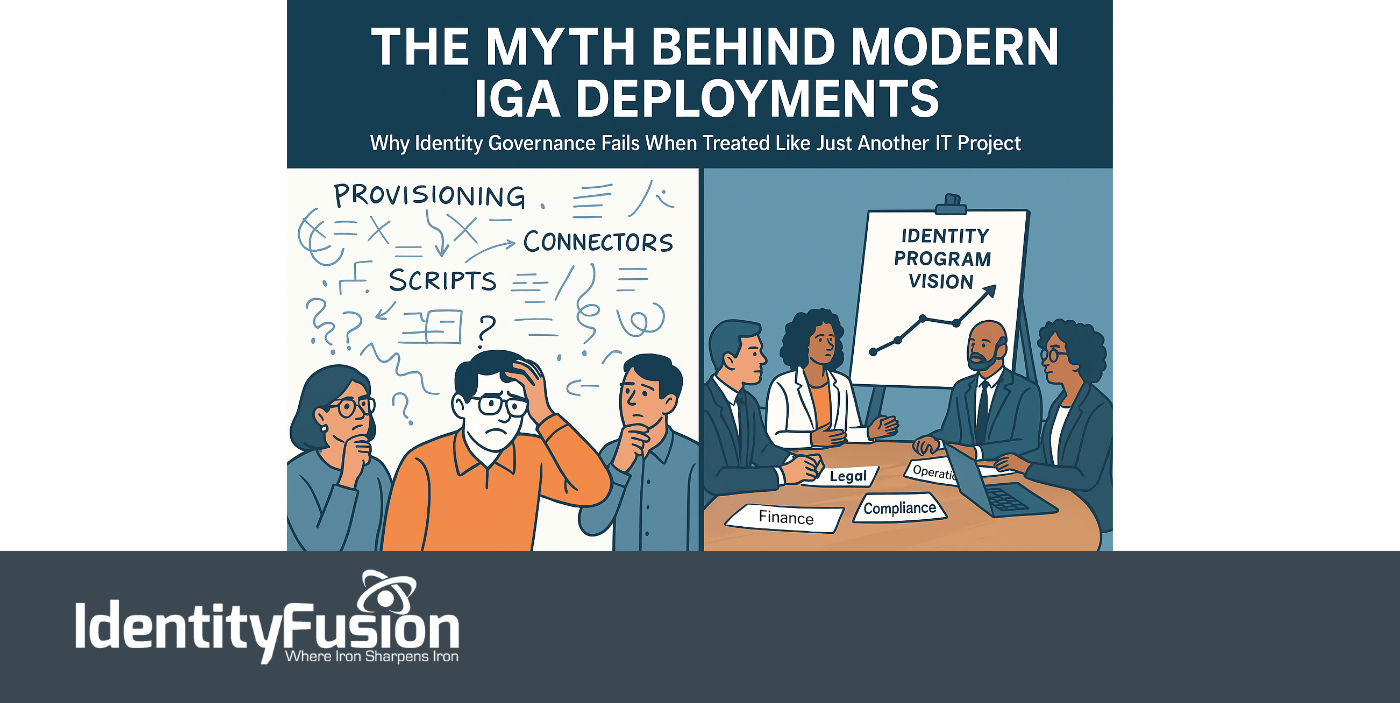
The Myth Behind Modern IGA Deployments
Identity is no longer just a security layer—it’s now central to everything an organization does. From onboarding employees and enabling partner collaboration to powering seamless..

Non-Human Identities: The Fastest-Growing Threat in IAM and Cybersecurity
In today’s digital battlefield, not all users are flesh and blood. In fact, most aren’t. The silent majority behind modern infrastructure, the service accounts, machine..
.png)
Secure Your Privileged Credentials: The Role of Credential Vaulting in PAM
Today, protecting privileged credentials is more critical than ever. Privileged credentials are essentially the keys to an organization’s most sensitive data and systems. When..

The Importance of Just-in-Time Access in Privileged Access Management
In today’s interconnected and data-centric world, organizations face escalating threats to their critical systems and sensitive data. Privileged accounts, with their elevated..
